INSTITUTIONAL ACCESS (SHIBBOLETH)
HOW INSTITUTIONAL ACCESS WITH SHIBBOLETH WORKS
Institutional subscribers using Shibboleth for identity management can use that authentication method to access Web of ScienceTM products and EndNote® online. Shibboleth authentication can be used to remain .compliment or replace existing authentication methods, such as IP or token.
Setting up access involves the following steps:
- First, the institution must belong to a supported federation. If the institution’s federation is not listed here, the institution must request a new federation setup through their sales representative. This can take several weeks.
- If the institution belongs to an existing federation, they can submit the setup request. This can take a few business days. A notification is sent to the contact indicated in the setup request via email.
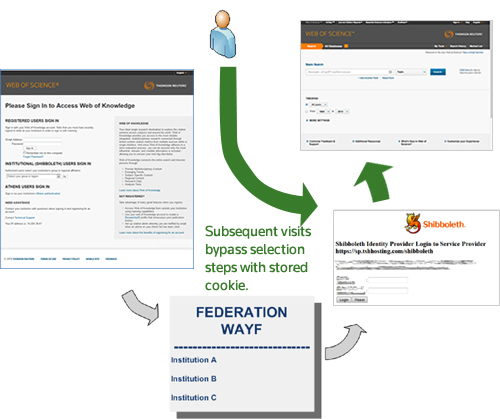
WAYF ACCESS
Users can access Web of Science using the existing links provided by their institutional resources. Upon access, they will receive an error that they are not authenticated and are given alternate options. They can click the Shibboleth link which directs them to federation selection page. After selecting their federation, they are directed to the federations’ WAYF (Where Are You From) server. The user selects their institution, logins, and is redirected back to the Web of Science application. The Federation and Identity Provider information is saved so that the user is not prompted to make these selections upon subsequent visits. Clearing cookies will remove this saved information.

WAYFLESS ACCESS
An institution can customize the links to Web of Science products and EndNote online include the encoded federation and IDP information in the URL, bypassing these selection steps upon access. The user is prompted to login with their institutional credentials and is directed back to the appropriate application.
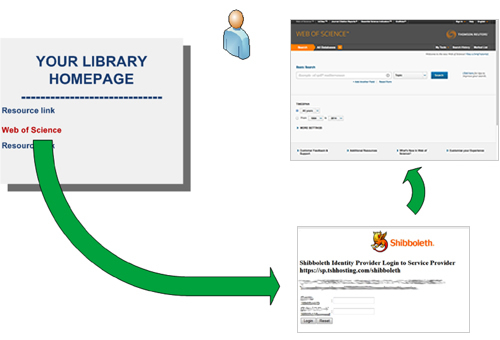
An institution can request the WAYFLESS URLs appropriate to their subscription through the setup request form.
USAGE REPORTING
Shibboleth access is logged to the subscribing institution’s monthly usage activity just as it would be for token or IP access. This activity appears in the usage reporting data as its own entry when running a custom report that includes the option to “Include User Credentials.”